A Florida journalist who is under criminal investigation for intercepting, recording and distributing raw video files of Fox News programming used a username and password belonging to CBS News to carry out the deed, The Desk has learned.
The journalist, Timothy Burke, discovered the credentials on the website of a Tennessee-based news radio station after the outlet accidentally published their internal list of usernames and passwords to a number of third party services.
Those passwords included credentials to LiveU Matrix, a cloud-based video delivery serviced used by a number of major broadcast outlets, including CBS News, Fox News and a television production company operated by former Fox News personality Tucker Carlson.
Federal prosecutors believe Burke misappropriated those login credentials to surreptitiously record raw video feeds of Carlson’s show and other Fox News programs, then quietly gave those video clips to Vice News and Media Matters for America, which published them without attributing Burke as their source.
The video files included one in which Carlson suggested Fox News should not employ executives who list pronounces on their social media accounts, and another that contained unedited and unaired footage of an interview between Carlson and Kanye “Ye” west in which the rapper made anti-Semitic comments.
Months after the articles were published, federal law enforcement officers raided Burke’s home, seizing numerous computers, cellphones, hard drives, notebooks and other items. Since then, Burke and his legal team have pursued the matter on two fronts — one in the court of law, the other in the court of public opinion — through which he continues to assert no legal wrongdoing.
Shortly after the raid on his home, the Tampa Bay Times newspaper filed a motion in federal court that sought access to the search warrant and an FBI affidavit in support of it. Burke later filed his own motion seeking to have the items seized by the FBI returned to him.
In court records reviewed by The Desk, Burke and his attorneys say the FBI and the U.S. Department of Justice (DOJ) wrongly targeted Burke for committing acts of journalism. They contend Burke was able to access raw video feeds from news organizations by accessing publicly-available web streams that were not encrypted, and thus he committed no crime. They also say Burke should not be investigated for cyber crime offenses because any usernames and passwords he used were available on the open Internet for anyone to see.
But other documents reviewed by The Desk and interviews conducted with several sources reveal Burke took advantage of numerous security and technological mistakes made by small and large broadcasters alike, then engaged in a public relations campaign in which they misled reporters into thinking the criminal investigation was a case of government overreach.

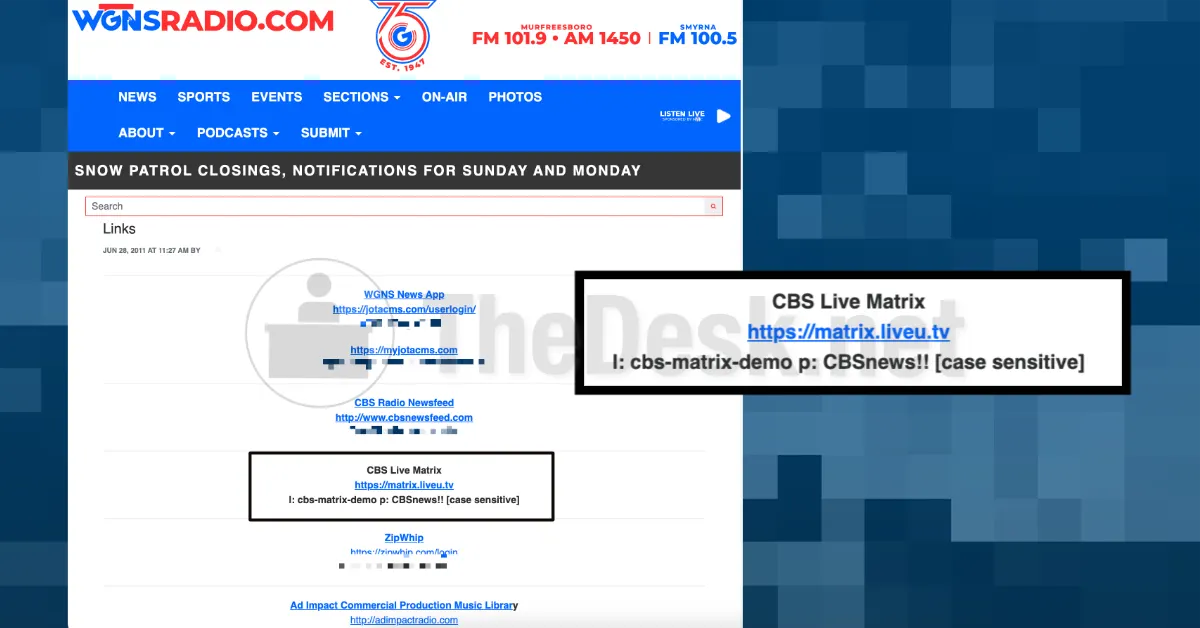
The situation began two years ago, when a news producer with radio station WGNS (1540 AM) updated a list of usernames and passwords that were stored on the station’s content management system and were intended for internal use.
The list included credentials to a number of services, including the WGNS news app, the CBS Radio news feed and a text message service called ZipWhip, according to a copy of the list obtained and reviewed by The Desk.
The list also included a username and password to LiveU Matrix, which was supplied by CBS News for use by CBS News Radio affiliates, of which WGNS is one. Both the username and the password contained the words “CBS News,” while the username also included the word “demo,” the list showed.
In an interview with The Desk last month, WGNS President Scott Walker said the credentials were supplied by CBS News at the start of the coronavirus health pandemic, and were intended to be used by CBS News radio stations who wanted direct access to press conferences and other live events related to the pandemic.
“I personally don’t know why a generic username and password would be sent to multiple outlets, but again, it was my understanding that is what occurred,” Walker said in an email to The Desk. “Furthermore, I don’t know what was accessible upon logging in, as we did not have much of a need for the different feeds. Our focus throughout COVID was local, not national.”
Still, the LiveU Matrix password made its way onto the internal list of credentials. The credentials were stored on a content management system that the station used for a number of purposes, including to publish news to its website, according to a source familiar with its operation.
At some point, a news producer tasked with maintaining the list accidentally changed its status from “private” to “public,” and the list was published online. The issue was caught within a few days, the source said, but by then, a version of the list had been saved by search engines and other services that provide archived versions of web pages.
In court documents, Burke’s lawyers contend that an anonymous source tipped Burke off to the list. For reasons that are still unclear, Burke didn’t reach out to anyone at WGNS about the list; instead, he took the username and password, and logged on to the LiveU Matrix.
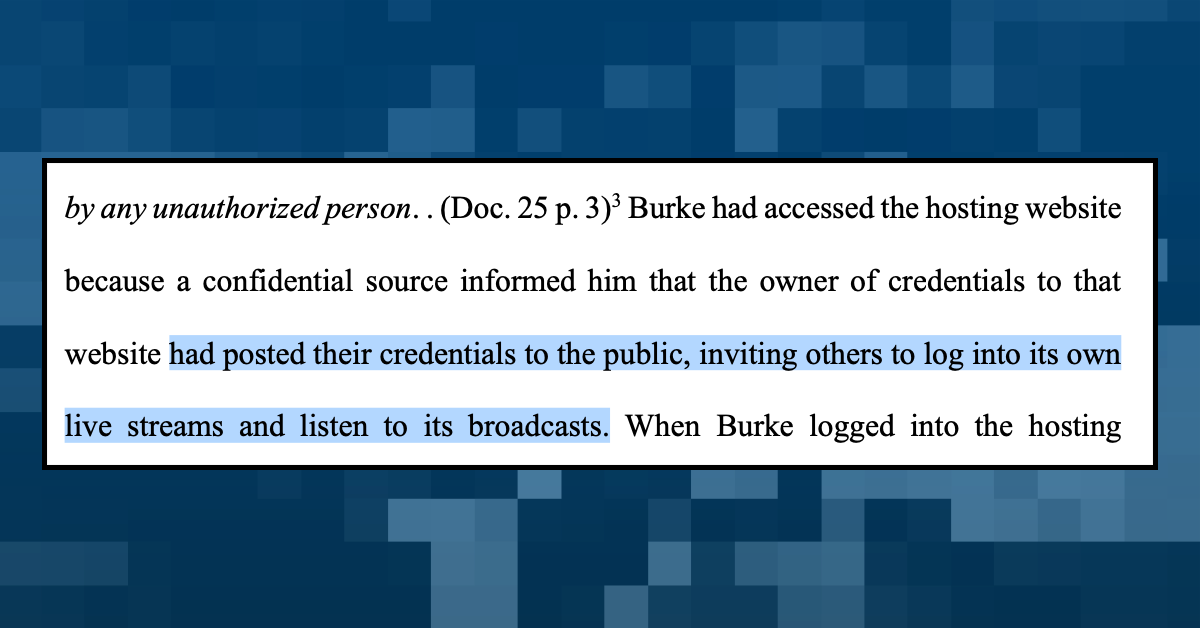
In an opening brief made to the appellate court last month, Burke’s lawyers contend that his use of the username and password was not unauthorized because the radio station “had posted their credentials to the public, inviting others to log into its own live streams and listen to its broadcast.”
A cached version of the website shows that statement is wrong: Nowhere did WGNS encourage its listeners to use any of the passwords provided in the list. Walker asserts the same, saying the radio station would never have invited its audience to use its internal passwords to access programming provided by others.
“We only invite our audience to listen to our live audio stream — the WGNS streaming audio is at the top right of our website…and it is free for listeners to access and does not require any log-in credentials,” Walker wrote. “Our streaming audio has always been free and has never required a login … I don’t recall a time that we have ever told listeners or website visitors to listen to another media outlet’s streaming service. We just wouldn’t do that.”
In any case, Burke did use the password to the LiveU Matrix, one of his attorneys revealed in a July letter sent to a federal prosecutor assigned to the case. In the letter, Mark Rasch claims Burke didn’t have direct access to Fox News video feeds until the LiveU Matrix “downloaded…[a text] file containing the list of visible and accessible live video feeds,” which was apparently done automatically.
“The list of feeds was available to anyone who logged into the site, including anyone with any demo account,” Rasch contends.
Numerous sources dispute this, including several television producers and broadcast technicians who regularly use the LiveU Matrix. They say the service only offers access to feeds that they are authorized to receive — because they belong to a certain group of stations, or are affiliated with a news service or wire — and that the LiveU Matrix does not download anything without a specific prompt.
A former LiveU engineer who worked on several iterations of the LiveU Matrix also claims the lawyer is wrong, claiming that the service — which is accessed through an ordinary web browser — only downloads a cookie file that keeps a person or station signed in to the service.
“It does not download anything, unless we tell it to download something, and even then, it’s only a video file,” said the engineer, who asked to remain anonymous because they did not have permission from their news organization to speak with a reporter. “I’ve never seen it download a list of feeds, even within our company. He’s totally wrong, it just does not work that way.”
It was not clear how Burke’s attorneys came to believe that the LiveU Matrix downloaded anything upon logging in, or whether they were simply passing along anecdotal and unsubstantiated claims from their client. Burke’s attorneys have refused to speak with The Desk about the case; as this story was coming together, a marketing firm hired by Burke’s legal team offered to arrange an interview with his latest attorney, Ryan Kirkpatrick, who is representing him pro bono. After accepting the invitation, Kirkpatrick reneged on the offer without explanation.
As of Monday, Burke has not been charged with a crime. But court briefs filed by his legal team in the pre-indictment stage reveal some of his legal defense should prosecutors move forward with charges in the future.
In an opening brief filed with an appellate court last month, the journalist’s legal team relied heavily on a recent U.S. Supreme Court case in which a former police officer’s computer fraud conviction was tossed. In that case, the higher court found Nathan Van Buren did not violate the Computer Fraud and Abuse Act when he accessed a police database to look up license plate information on behalf of another person. The court held that Van Buren was authorized to access the database as part of his job, even if he exceeded the type of authorization that his employer intended.
But Burke’s situation is different from Van Buren, because he has no apparent connection to any of the parties involved in the investigation. In an email, Walker at WGNS Radio said he had “never heard of Timothy Burke” until he was contacted by The Desk, and further said that “Timothy Burke has never been employed or contracted by WGNS, to my recollection.” A spokesperson for Fox News affirmed the same, writing by e-mail that “I can confirm that Tim Burke has never been employed by Fox News Media,” referring to the parent company of the news channel.
Officials at LiveU and CBS News did not return requests for comment, but a public resume posted to Burke’s website and LinkedIn profiles do not mention any employment or contractual work for either company.